Website Security
Putting a website on the Internet is exposing it to hacking attempts, port scans, traffic sniffers and data miners. If you are lucky, you can also get legitimate traffic, but not if someone destroys or alters your site first. Most of us know that you need to look for the lock icon when you are browsing to make sure a site is secure, but it only scratches the surface of what can be done to protect a web server. Even the SSL protocol itself can be used in different ways, some being much better than others. Cookies store sensitive information from websites; securing these can prevent identity theft.
Click here to download Free Internet Security
In this guide to website security, we will give you the knowledge you need to protect your website. We’ll look at common threats, what you can do to protect your website against them and the most secure web hosts. We do not talk much about the security of websites, but it is an extremely important topic. Even small websites are becoming the target of malware attacks, spam and distributed denial of service attacks, used to steal private user data or to spread malware.
Website security is an essential part of protecting and securing websites and servers. Web sites are scanned for possible vulnerabilities and malware using security software. This software can search for backdoor hackers, redirect hacks, trojans and many other threats. Website security software notifies the user if the website poses a problem and provides solutions to resolve it. it is a system of protection measures and protocols that can protect your website or web application against hacking or seizure by unauthorized personnel. This integral division of information security is essential to the protection of websites, web applications and web services. Everything that is applied on the Internet should have some form of web security to protect it.
Why is website security important?
Website security is important because no one wants to have a website hacked. Having a secure website is as vital to someone’s online presence as having a website host. If a website gets hacked and blocked, for example, it loses up to 98% of its traffic. Not having a secure website can be as bad as not having a website at all, if not worse. For example, a customer data breach can result in lawsuits, heavy fines, and a ruined reputation.
Why should you care about website security?
Cyber attacks against public websites of any size are commonplace. An attack on your website could
- Cause defacement,
- Cause a denial of service (DoS) condition,
- Allow the attacker to obtain sensitive information, or
- Allow the attacker to take control of the affected website.
Website security protects your website from:
- DDoS attacks: These attacks can slow down or completely block your site, making it inaccessible to visitors.
- Malware: In short, “malware”, the malware is a widespread threat used to steal sensitive customer data, distribute spam, allow cyber criminals to access your site, etc.
- Blacklist: Your site may be removed from search engine results and signaled by a warning that diverts visitors if search engines detect malware.
- Vulnerability exploits: Cyber criminals can access a site and the data stored there by exploiting the weak points of a site, such as an outdated plugin.
- Defacement: This attack replaces the content of your website with the malicious content of a cyber criminal.
How to Keep Your Website Safe
Use a Firewall
Internet is, in a word, unreliable. The server on which your website is host is trustworthy or, at least, we hope. However, it is usual to connect the rest of the unsecure internet to your online files. Not protecting it, especially with web hosting, allows potential viruses to get too close. This is where a firewall comes in.
Imagine that there is a fire and that you have a brick wall to protect yourself. That’s basically what a firewall does. Web hosts use two forms to protect your website.
Enable DDoS Protection
Firewalls help combat DDoS attacks by detecting IP spoofing long before a simulated attack can be made. In the case of a botnet, however, all IP addresses are unique. A firewall can not be maintained because traffic entering and leaving your website seems legitimate, but at a higher rate.
This is why DDoS protection exists or, more specifically, the mitigation of DDoS attacks. DDoS attacks attempt to crash a web server by flooding it with traffic. With a content distribution network this traffic can be dissociated to traverse a distributed network of servers and absorb the impact.
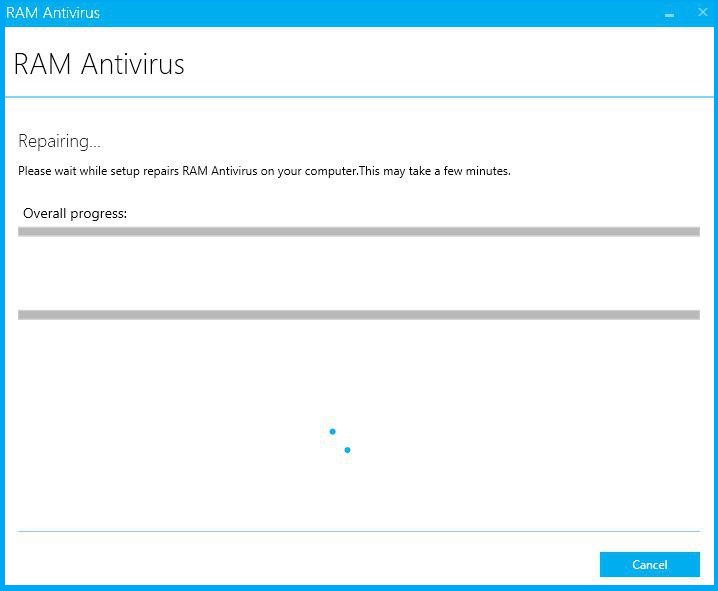
Install an Antivirus and Clean Your Website
You can install RAM Antivirus on your computer and get to work, there are dedicated monitoring and cleaning tools for websites. Using one can mean the difference between a compromised website and a healthy website.
How can you improve your cybersecurity protection against website attacks?
Organizations and individuals can protect their websites by applying the following best practices to their web servers:
- Apply the principle of least privilege- Ensure that all users have minimal privileges on the Web server (including interactive end-users and service accounts).
- Use multifactor authentication-Implement multifactor authentication for user connections to Web applications and the underlying website infrastructure.
- Change the username and password of the default provider-The default provider credentials are not secure – they are usually readily available on the Internet. Changing the default user names and passwords will prevent an attack using the default credentials.
- Disable useless accounts-Disable accounts that are no longer need, such as guest accounts or individual user accounts that are no longer use.
- Use the security checklists-Audit and reinforce configurations based on application-specific security checklists on the system.
- Use the white list of applications-Use RAM Application Scanner to whitelist and disable modules or features that offer features that are not needed for business purposes.
- Also, Use network segmentation and segregation-Segmentation and network segregation make it more difficult for attackers to move sideways in connected networks. For example, placing the Web server in a properly configured demilitarized zone limits the type of network traffic allowed between the systems in the DMZ and the systems in the internal corporate network.
People May Also Like…
Data protection
What is the data protection Data protection has grown to be of utmost importance to both individuals and organizations in the connected. world of today, where information travels quickly across many digital
What is a security software
Security software It is impossible to overstate the value of strong security software in today's digital world. Individuals and organizations must take proactive measures to safeguard their sensitive data and defend against
Website reputation analysis
Website reputation analysis Websites are incredibly important for establishing an online presence for businesses, organizations, and people in the modern world. Analysis and evaluation of a website's reputation are crucial because there are
What is a Virtual private network (VPN)
What is a virtual private network (VPN) Virtual private network (VPN) have become an essential tool for both individuals and businesses in a time when online privacy and security are of the








