Security Threats
What is a Security Threat?
The security threat is defined as a risk that could potentially harm computer systems and the organization. The cause may be physical, such as a person stealing a computer containing vital data. The cause could also be non-physical, such as a virus attack. In this, we will define a threat as a potential attack by a hacker that may allow them to gain unauthorized access to a computer system.
Click here to download Free Antivirus
It’s a dangerous world on the Web. Just as your mother may have told you never to speak to strangers, the same advice applies to the virtual world. You may know that foreigners should not be given the details of your professional bank account. But can you be sure that the website you are connecting to is your bank’s website and not a fake created by a cyber criminal?
Threats to IT security are always inventive. Masters of disguise and manipulation, these threats are constantly evolving to find new ways to hinder, steal and harm. Arm yourself with information and resources to protect against complex and growing threats to IT security and stay safe online.
Examples of security threats
Remember that a threat is very general. It does not include how to achieve it, or even if it is possible in the current system. Here are some examples.
- A malicious user reads files from other users.
- An attacker redirects requests sent to a web server to his own web server.
- An attacker modifies the database.
- A remote attacker executes commands on the server.
Each of these examples can easily be associated with a category in STRIDE. Other examples would be malware, Trojans and worms.
The most common network security threats
-
Computer virus
A computer virus is a small piece of software that can spread from one infected computer to another. The virus could corrupt, steal or delete data on your computer, or even erase everything from your hard drive. A virus could also use other programs, such as your email program, to spread to other computers.
-
Rogue security software
Taking advantage of the fear of computer viruses, fraudsters have discovered a new way to commit fraud on the Internet. Unreliable security software is malicious software that misleads users into believing that a computer virus is installed on their computer or that their security measures are not up-to-date. They then propose to install or update the user’s security settings. They will either ask you to download their program to remove the suspected viruses, or to pay for a tool. In both cases, malware is installed on your computer.
-
Trojan horse
Metaphorically, a “Trojan Horse” is to induce someone to invite an attacker to a protected area in a secure manner. In computer science, this has a very similar meaning: a Trojan horse, or “Trojan horse”, is a code or attacking malware that prompts users to perform it of their own free will by hiding behind a legitimate program.
They often spread by email; it may be an e-mail sent by someone you know. When you click the email and its attachment, you immediately downloaded malicious software to your computer. Trojans also spread when you click on a fake advertisement.
-
Malicious spyware:
Malicious spyware is used to describe the Trojan horse application created by cyber criminals to spy on their victims. An example would be a keylogger software that records every keystroke of a victim on its keyboard. The recorded information is periodically returned to the original cyber crime on the Internet. The record capture software is widely available and is intended for parents or businesses wishing to monitor the use of the Internet by their children or employees.
5. Rootkits
Rootkits are among the most difficult to detect. They are activated at system startup, before the antivirus software starts. Rootkits allow the installation of files and accounts, or the ability to intercept sensitive information.
6. Network Spoofing
Network spoofing occurs when hackers set up fake access points (connections that look like Wi-Fi networks but are actually traps) in crowded public places such as cafes, libraries, and airports. Next, cyber criminals assign access points to common names, such as “Free Airport Wi-Fi” or “Coffeehouse,” which encourage users to sign in. In some cases, attackers ask users to create an “account” to access these free services, with a password.
-
Spam
Spam in the security context is mainly used to describe unwanted email – unwanted messages in your inbox. Spam, or spam, is a nuisance because it can clutter your mailbox and potentially take up space on your mail server. The unwanted advertising items you do not like are relatively harmless. However, spam may contain links that, once clicked, can go to a website that installs malware on your computer.
How to Arm Yourself Against These Threats
The list of threats to system security is long and growing. A defense strategy that includes antivirus software, system patches, and timely software updates is essential to combat this problem. For system administrators and end users, understanding the differences between these threats is the first step toward removing these threats.
- Use strong authentication
The passwords are outdated. Password removal technology is advanced enough and stronger passwords generate forests of sticky notes on monitors. And many employees share passwords. The alternatives are expensive and the overall deployment is beyond the means of most organizations.
- Secure your desktops
You can not rely on users to be responsible for all their configurations, but if you use the Microsoft Active Directory service, you can use Group Policies to lock your organization’s workstations.
- Monitor misuses
Your security may require direct monitoring of employees, from video cameras to logging keystrokes. Research suggests that up to one-third of employers do this to some extent.
Tips for threats Security
For best computer security, you must follow certain guidelines, which are also called computer best practices.
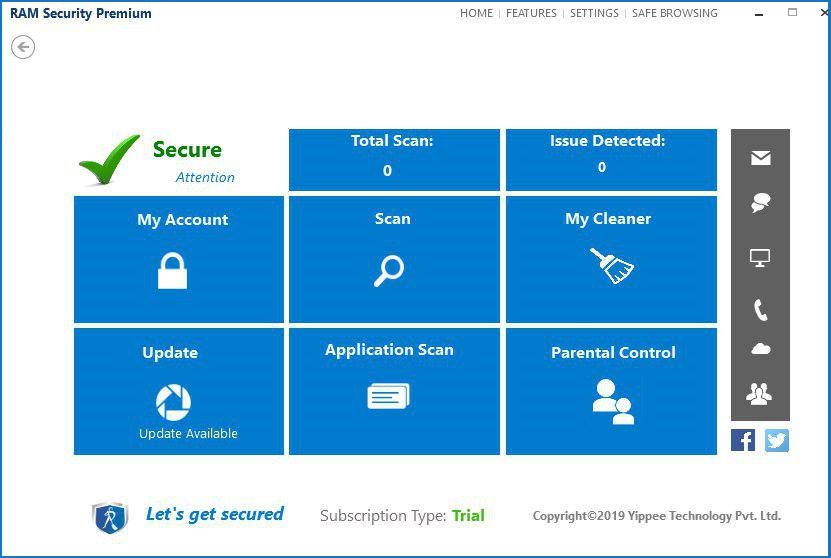
- Use the best antivirus software, which not only provides protection to your PC but also internet protection and guards against cyber threats. For this, you can completely rely on RAM Internet Security. It will greatly help in detecting and removing malware, but it will not help much if you do not keep the software, and all your other programs updated.
- Do not download untrusted email attachments and these may carry harmful malware.
-
Never download software from unreliable sites as they may come with a virus that may infect your system as soon as you install the software.
People May Also Like…
Operating System (OS) security
Securing Operating System: Protecting Digital Environments In the rapidly changing world of technology, operating system (OS) security is a vital line of defence against online attacks. Operating system security is the first line of defence
Data protection
What is the data protection Data protection has grown to be of utmost importance to both individuals and organizations in the connected. world of today, where information travels quickly across many digital
What is a security software
Security software It is impossible to overstate the value of strong security software in today's digital world. Individuals and organizations must take proactive measures to safeguard their sensitive data and defend against
Website reputation analysis
Website reputation analysis Websites are incredibly important for establishing an online presence for businesses, organizations, and people in the modern world. Analysis and evaluation of a website's reputation are crucial because there are







