What is Coronavirus Malware And How to Prevent it?
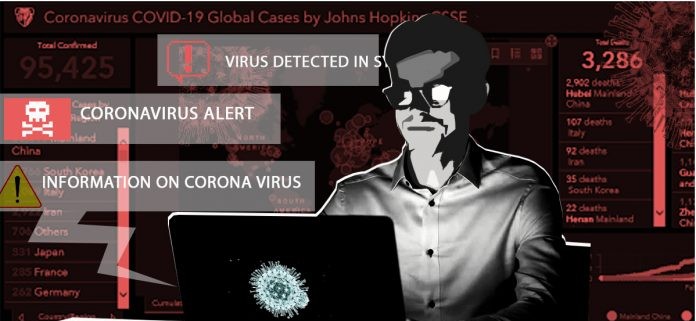
To say that 2020 “has been interesting” so far would be an understatement. While there are many unknowns to come, one thing the cyber community knows all too well is that unrest and disruption is a prime time for cyberattacks. coronavirus malware
Whether it’s a hurricane, an election, or the current state of a pandemic, cybercriminals profit from the mess. As we see an increase in cybercrime activity due to COVID-19, let’s take a look at emerging cyber threats and preventative measures.

Types of cyberattacks
Malicious domains: There are a considerable number of domains registered on the Internet which contain the terms: “coronavirus”, “corona virus”, “covid19” and “covid-19”. Although some are legitimate websites, cybercriminals create thousands of new websites every day to conduct spam, phishing, or malware campaigns.
Malware: Cybercriminals are taking advantage of widespread global communications about the coronavirus to mask their activities. Malware, spyware and Trojans have been found embedded in interactive coronavirus maps and websites. Spam emails also trick users into clicking links that download malware to their computers or mobile devices.
Ransomware: Hospitals, medical centers and public institutions are targeted by cybercriminals for ransomware attacks – as they are overwhelmed by the health crisis and cannot afford to be excluded from their systems, criminals think they are. likely to pay the ransom. The ransomware can enter their systems through emails containing infected links or attachments, compromised employee credentials or by exploiting a system vulnerability.
How attackers exploit the COVID-19 crisis
-
Phishing emails
Email is and will remain the main threat vector for people and organizations. Cybercriminals have long used global events in phishing campaigns to increase their success rate, and the coronavirus is no exception.
-
Malicious applications
Although Apple has placed limits on COVID19-related apps in its App Store and Google has removed some apps from the Play Store, malicious apps can still pose a threat to users. DomainTools discovered a site urging users to download an Android app that provides tracking and statistical information on COVID-19, including heat map visuals.
-
Defective domains
New websites are quickly being created to disseminate information relating to the pandemic. However, many of them will also be traps for unsuspecting victims. Recorded Future reports that hundreds of domains related to COVID-19 have been registered every day for the past few weeks.
-
Endpoints and insecure end users
With large numbers of employees or even all businesses working remotely for an extended period of time, the risks around devices and the people who use them increase. Devices that staff use at home could become more vulnerable if employees do not regularly update their systems.
-
Vulnerabilities among suppliers and third parties
Every partner, customer, and service provider in your ecosystem is likely facing the same issues as your organization. Liaise with critical parts of your third-party ecosystem to ensure they take action to secure their remote workforce.
-
Communication and home work applications
New ways of working present new opportunities for attackers. The massive increase in remote working and collaboration tools means that their Security is now a major concern. The growing popularity of Zoom ultimately led the company to freeze product development to address security concerns, and according to Vice, interest in zero day exploits related to Zoom and other collaborative applications is “very high ”with forwards.
-
Target healthcare organizations and COVID hotspots
Although hacking groups have vowed not to do so, healthcare organizations are under increasing attack. At the start of the pandemic, the Illinois public health website was hit with ransomware, coronavirus malware while the Department of Health and Human Services (HHS) suffered a DDoS attack attempt.
-
Harnessing future spinoffs and recovery
Mimecast predicts that due to the cancellation of a number of events, such as the 2020 Olympics, it is highly likely that future cyber campaigns will focus on using the lure of recovery. expenses to elicit interaction with malicious content.
How to prevent phishing:
- Check their email address
- Make sure the sender has an email address such as “[email protected]”
- If there is anything other than “who.int” after the “@” symbol, that sender is not from WHO. For example, WHO does not send emails from addresses ending in “@ who.com”, “@ who.org” or “@ who-safety.org”
- Be careful though, even an email address with the correct domain name may not come from WHO. Criminals can spoof the “From” address on emails to make them appear as “@ who.int”. Please follow steps 2-6 below to avoid phishing.
- WHO has implemented a new e-mail security control called Domain Message Authentication, Notification and Compliance (DMARC) to significantly reduce this type of identity theft.
- Check the link before clicking
- Make sure the link starts with “https://www.who.int”. Better yet, go directly to the WHO website by typing “https://www.who.int” into your browser.
- Be careful when providing personal information
- Always consider why someone wants your information and if it is appropriate. There is no reason why someone would need your username and password to access public information.
- Don’t rush and feel pressured
- Cybercriminals use emergencies such as the coronavirus disease pandemic (COVID-19) to trick people into making decisions quickly. Always take the time to think about a request for your personal information and whether the request is appropriate.
- If you’ve given out sensitive information, don’t panic
- If you believe that you have given data such as your username or passwords to cybercriminals, immediately change your credentials on each site where you have used them.
- And If you see a scam, report it.
People May Also Like…
Data protection
What is the data protection Data protection has grown to be of utmost importance to both individuals and organizations in the connected. world of today, where information travels quickly across many digital
What is a security software
Security software It is impossible to overstate the value of strong security software in today's digital world. Individuals and organizations must take proactive measures to safeguard their sensitive data and defend against
Website reputation analysis
Website reputation analysis Websites are incredibly important for establishing an online presence for businesses, organizations, and people in the modern world. Analysis and evaluation of a website's reputation are crucial because there are
What is a Virtual private network (VPN)
What is a virtual private network (VPN) Virtual private network (VPN) have become an essential tool for both individuals and businesses in a time when online privacy and security are of the